We have over 100 web-based resources and services in our Library, but there may be times when you need to get connected to an API that isn't currently supported. Here we'll show you how to use Temboo to make HTTP requests to any API using our Utilities > HTTP Choreos.
Not all APIs require require authentication, but many of them do. Understanding the authentication mechanism that an API uses is often the first step when getting started. The most common authentication schemes are:
When an API uses Basic Authentication, you can simply authenticate using your username and password. The Utilities > HTTP Choreos expose inputs for Username and Password, and generate a Basic Authentication token for you. In the HTTP request that is performed when running these Choreos, your username and password are concatenated, Base64 encoded, and passed into the Authorization header like this:
Authorization: Basic QWxhZGRpbjpvcGVuIHNlc2FtZQ==
The above token is the Base64 encoded string representing the username/password combination: Aladdin:open sesame.
Another common authentication scheme is key-based authentication. This is when an API issues a key that identifies your application and authenticates you with the service. An API Key can be specified in a query parameter, header parameter, or even in the base URL.
API Key sent as a query parameter name/value pair:
https://www.googleapis.com/youtube/v3/search?key=your_api_key
API Key sent as a header parameter name/value pair, along with the Accept header:
X-M2X-KEY: your_api_key Accept: application/json
API Key sent as part of the base URL for a request:
http://api.wunderground.com/api/your_api_key/conditions/q/CA/San_Francisco.json
OAuth 2.0 is the most preferred method for API authentication when applications need to access data on behalf of a user. The protocol allows a user to authorize third-party access to their resources without sharing their credentials. It is used by Google, GitHub, Facebook, Microsoft, and countless other web services.
If you are working with an API that uses OAuth 2.0, you can use the Utilities > Authentication > OAuth2 Choreos to authenticate a user and retrieve access tokens.
In the HTTP bundle, you'll find Choreos for the most common HTTP methods used in API requests:
When using the HTTP Choreos, request data is specified in one or more of the following inputs:
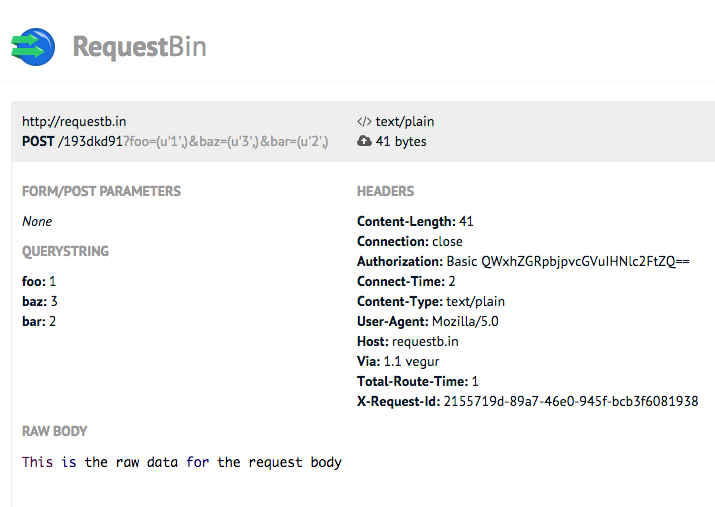
A good way to test these Choreos is to use RequestBin - a service that makes it easy to inspect HTTP requests. Follow the steps below to make a POST request to RequestBin and inspect the request data.
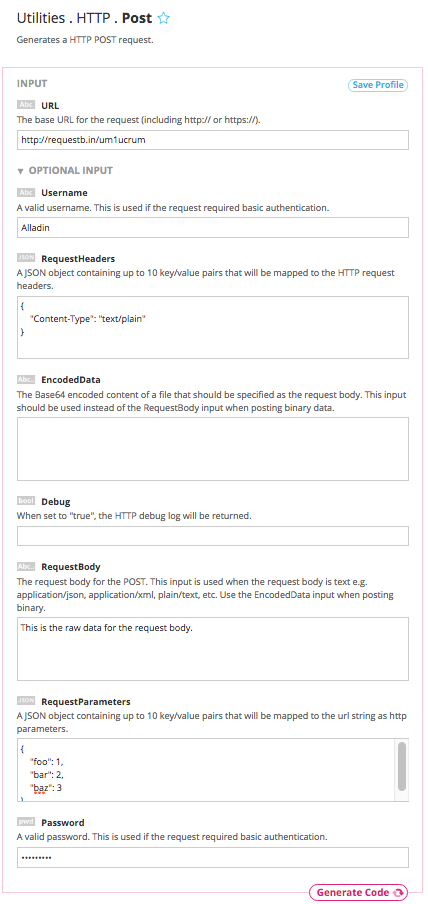
With an input set like this, you will see the name/value pair sent in the RequestParameters listed as the query string received. You will also see the Content-Type and Authorization headers received since the RequestHeaders, Username, and Password were specified. Finally, the data specified in the RequestBody input should be listed as the Raw Body in RequestBin.
Now you're ready to run any of our HTTP Utilities and start connecting to any API. You're just a few steps away from making something extraordinary!
Once you've got your code up and running, you're ready to move on and do more. From monitoring your running applications, to moving your generated Temboo code to your preferred development environment and sharing it with colleagues, collaborators and friends - we've got you covered.
We're always happy to help. Just email us at support@temboo.com, and we'll answer your questions.